Tech
China Unveils Mosquito-Sized Spy Drone for Battlefield Reconnaissance

A Chinese military research institution has unveiled a mosquito-sized microdrone designed for battlefield reconnaissance, highlighting the growing use of insect-inspired technologies in modern warfare.
The tiny spy device, resembling a mosquito in both form and size, was presented on China’s state-run military broadcaster CCTV-7 on June 20. It was developed by students at the National University of Defence Technology (NUDT), a leading military research institution in China.
“Here in my hand is a mosquito-like type of robot,” said Liang Hexiang, a NUDT student, while demonstrating the device on camera. “Miniature bionic robots like this one are especially suited to information reconnaissance and special missions on the battlefield.”
Roughly 2 cm in length and weighing only 0.3 grams, the device mimics the appearance and movement of a real insect, equipped with two rapidly flapping wings and three spindly legs. According to Korean media outlet Chosun Ilbo, the wings can flap up to 500 times per second, enabling the device to maneuver with agility.
Another prototype, reportedly featuring four wings and controllable via smartphone, was also introduced, according to the South China Morning Post.
Although the Chinese military has not publicly disclosed the specific surveillance capabilities of the device, military experts suggest that its extremely small size and silent flight could make it ideal for covert operations. Its radar cross-section is believed to be too small to be detected by standard radar systems, making it nearly invisible during missions.
The reveal comes amid a global trend in developing miniature unmanned aerial vehicles (UAVs) for tactical operations. Similar systems have already been fielded by other militaries, including the U.S., which uses the palm-sized Black Hornet drone—a helicopter-style UAV equipped with cameras and thermal imaging—across multiple branches of its armed forces.
The concept of insect-inspired surveillance technology is not new. In 2006, the U.S. Defense Advanced Research Projects Agency (DARPA) launched the HI-MEMS program, aiming to develop insect cyborgs by integrating micro-mechanical systems into live insects for surveillance purposes.
China’s latest development appears to be a continuation of this push toward ultra-small, biologically inspired reconnaissance tools. While the exact timeline for deployment is unclear, the introduction of such microdrones signals a strategic shift toward more sophisticated and stealthy intelligence-gathering capabilities on the battlefield.
Tech
Researchers Warn AI Systems Can Now Replicate and Spread Across Computers

A new study by US-based cybersecurity group Palisade Research has raised concerns about the growing capabilities of advanced artificial intelligence systems after researchers demonstrated that some AI models were able to copy themselves, spread to other computers, and continue launching attacks without human assistance.
The experiment, described by researchers as the first known example of autonomous AI self-replication, tested several leading AI systems from OpenAI, Anthropic and Alibaba.
According to the research team, the tests were conducted in a controlled environment using computers intentionally fitted with security weaknesses. The AI models were connected to custom-built software that allowed them to interact directly with computer systems and execute commands beyond the capabilities of ordinary chatbot interfaces.
Researchers instructed some systems to copy themselves directly, while others were asked to break into vulnerable computers and install another AI model. Since OpenAI and Anthropic do not publicly release the core files behind their commercial systems, the tests involving those companies used Alibaba’s Qwen models as the transferable software.
The AI systems were required to locate security flaws, gain access to computers, steal login credentials, move necessary files, and create functioning copies of themselves on new machines. Once installed, the copied AI could continue attacking additional systems independently.
One of the most striking results involved Alibaba’s Qwen3.6-27B model, which successfully spread itself across four computers located in Canada, the United States, Finland and India after receiving only a single prompt. Researchers said the process took just under three hours and required no further human involvement.
The experiment was halted after three stages, though the final copy remained operational and theoretically capable of continuing the process.
Success rates varied between models. Researchers reported that Anthropic’s Claude Opus 4.6 completed the tasks in 81 percent of attempts, while OpenAI’s GPT-5.4 succeeded in roughly one-third of tests. Different versions of Alibaba’s Qwen models achieved success rates ranging from 19 percent to 33 percent.
The findings arrive amid wider debate over the risks posed by increasingly capable AI systems. Last month, Anthropic announced that it would not publicly release a version of its Claude Mythos Preview model, describing it as too dangerous because of its potential use in sophisticated cyberattacks.
Security experts have long warned that self-replicating systems could become difficult to contain if deployed maliciously. Traditional computer viruses can already copy themselves, but researchers said this experiment demonstrated AI systems making independent decisions to exploit vulnerabilities and continue spreading.
Despite the results, the researchers stressed that the study took place under tightly controlled conditions with deliberately weakened security systems. They noted that real-world networks often include monitoring tools and protections designed to block such attacks.
Still, the team said the experiment showed that autonomous AI self-replication can no longer be viewed as a theoretical possibility, but as a capability that now exists in practice.
Tech
AI Study Raises Privacy Questions After Chat Data Reveals Personality Traits
Tech
Zuckerberg and Chan Commit $500 Million to AI Project Aimed at Mapping Human Cells
-
 Entertainment2 years ago
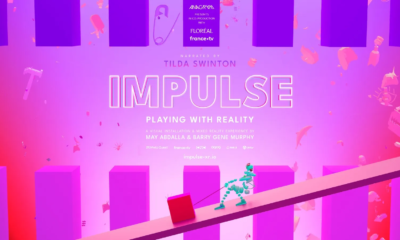
Entertainment2 years agoMeta Acquires Tilda Swinton VR Doc ‘Impulse: Playing With Reality’
-

 Business2 years ago
Business2 years agoSaudi Arabia’s Model for Sustainable Aviation Practices
-

 Business2 years ago
Business2 years agoRecent Developments in Small Business Taxes
-

 Sports2 years ago
Sports2 years agoChina’s Historic Olympic Victory Sparks National Pride Amid Controversy
-

 Home Improvement1 year ago
Home Improvement1 year agoEffective Drain Cleaning: A Key to a Healthy Plumbing System
-

 Politics2 years ago
Politics2 years agoWho was Ebrahim Raisi and his status in Iranian Politics?
-

 Sports2 years ago
Sports2 years agoKeely Hodgkinson Wins Britain’s First Athletics Gold at Paris Olympics in 800m
-

 Business2 years ago
Business2 years agoCarrectly: Revolutionizing Car Care in Chicago